Guys! I need the 3.14.0-beta2! can anybody help me?
Releases · elementor/elementor
The most advanced frontend drag & drop page builder. Create high-end, pixel perfect websites at record speeds. Any theme, any page, any design. - elementor/elementor
You MUST read the Babiato Rules before making your first post otherwise you may get permanent warning points or a permanent Ban.
Our resources on Babiato Forum are CLEAN and SAFE. So you can use them for development and testing purposes. If your are on Windows and have an antivirus that alerts you about a possible infection: Know it's a false positive because all scripts are double checked by our experts. We advise you to add Babiato to trusted sites/sources or disable your antivirus momentarily while downloading a resource. "Enjoy your presence on Babiato"
Guys! I need the 3.14.0-beta2! can anybody help me?
i also need the pro version =( but ty <3
Releases · elementor/elementor
The most advanced frontend drag & drop page builder. Create high-end, pixel perfect websites at record speeds. Any theme, any page, any design. - elementor/elementorgithub.com
Well, I don't use this myself, but I think it's a stretch to say it's fake and dangerous. I reviewed a lot of the code and looked for common indicators (base64, eval, etc) and didn't see anything, but of course there could be a million problems in plain site and with a large code base one just couldn't know. Both of these sites are just pointing to downloads at github:I think it's FAKE AND DANGEROUS. First and foremost question you should ask ...
It is very good to see such elaborate and thoughtful reply but I would encourage to see if there is any comment regarding the original post and what does it say, otherwise the whole point of such a thoughtful reply goes into vain. My point is @Medw1311 has already corrected me in this post here: https://babia.to/threads/elementor-pro-wordpress-websites-builder-premium.108/post-1223256 and @GambitSteel here: https://babia.to/threads/elementor-pro-wordpress-websites-builder-premium.108/post-1223325 and I have already apologized for not knowing the actual fact here: https://babia.to/threads/elementor-pro-wordpress-websites-builder-premium.108/post-1223580 . So, to avoid the irrelevancy of your thoughtful post, you should check first whether the topic has ended or not. In my case, I think with my apologizing, the topic was ended and because of that, your beautiful post became partly irrelevant. The point of my post was my skepticism or you can say 'paranoia' about using unauthorized nulled scripts. But I should thank you for the methods of security check you have written and you've rightfully mentioned that "I won't doing all that work" which is my thought also and that's why I avoid and discourage any member here to download resources outside this forum. If something goes wrong with the resources downloaded from here (accidents happen), at least we have a place and have good numbers of knowledgeable people to ask for help and they do help... a lot, believe me. Lastly, I should thank you for spending your precious time to reply and it is not a reply for the sake of reply... it's a very informative one. I will request you to visit this forum more often and if possible, write some guides on security check, taking precautions while creating websites and apps or testing scripts and how to check scripts properly because I think, you have some practical experiences on these things. I think I have not said anything rude in this post.Well, I don't use this myself, but I think it's a stretch to say it's fake and dangerous. I reviewed a lot of the code and looked for common indicators (base64, eval, etc) and didn't see anything, but of course there could be a million problems in plain site and with a large code base one just couldn't know. Both of these sites are just pointing to downloads at github:
(1) https://unlockelementor.tk/ - points to the 3.8.0 version (old)
(2) https://proelements.org/ - points to 3.13.2 version (newest)
These sites don't appear to add anything to nor change the releases from here:

Releases · proelements/proelements
This plugin enables GPL features of Elementor Pro: widgets, theme builder, dynamic colors and content, forms & popup builder, and more. - proelements/proelementsgithub.com
The question is, whether the github project is of pure intent and function and the code is working. I don't know. I do know that usually when people backdoor stuff on github it is found and reported and the whole account gets banned. I've personally reported a dozen different malware in github and seen the accounts closed, so I know it works. There are a couple of different ways to check for malware aside from code inspection, such as setting this up on a test site and then using security products to watch for changes in the filesystem and network traffic like outbound requests to a c2, things like that. (the plugin downloading secondary stage payloads, etc). I won't be doing all that work.
Also, based on the work those guys do when I look at the commit history and the length of time of the project, it would have to be a pretty elaborate trick if that's all it was.
Please Updated v3.14.8
Has it been released yet??!! According to this article here https://elementor.com/blog/introducing-313-new-css-grid-and-more/, Elementor developers have mentioned about version 3.13 only and if they release even the 3.14, they would have mentioned in their blog, don't you think?
Then I think you should ask Elementor Development Team for that version otherwise, according to your post, it is exclusively available to experts only. So, I wonder how it be available here??!! Babiato is a NULLING FORUM, not a 'TESTER'S FORUM' as per my knowledge. May be, I am wrong. Who knows?

Releases · elementor/elementor
The most advanced frontend drag & drop page builder. Create high-end, pixel perfect websites at record speeds. Any theme, any page, any design. - elementor/elementorgithub.com
You seem to be updating information very slowly.
Version 3.14 DEV has been released to developers
And version 3.14.8 is a desk session sent exclusively to experts for pre-test.
And I need this version to test, I don't get this latest version of Elementor
Read previous before postingThis version, 3.13.2 = no templates download, free or pro, and any page content is duplicated.
Fresh install, php 8, 256 ram, etc..
F Y I
3.13.0 version works fine all imports/downloads.
It appears only you know where the version is, so please share the link so that Babiato null masters can work their magic.Please Updated v3.14.8
Please read @Medw1311 post again, especially the highlighted part below:
Hi, where can I buy an elementor pro license for 5usd? Thanks!Well either will be safe.
But of course I'd actually recommend buying a genuine Elementor Pro Licence from me for $5 per year per site for the ultimate safety and security
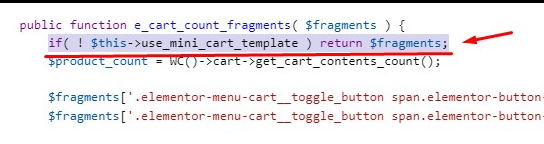
This incompatibility still plagues us and this fix is essential still in 2023 June - man I tell you someone wrote earlier "not all heroes wear capes" well jkrolling man I just want to say again how much I appreciate that you shared this fix because from what I see it's nowhere on the web and this one line fixes the minicart being broken on one of my customer sites who use Porto as their theme. Without this one line modification to Elementor the minicart wouldn't work, it would just have a spinning icon and be unusable. Hopefully the Elementor devs will find more of these incompatibilities and fix their code but in the meantime I patch each version with this line and include a thankyou to jkrolling in the comments. Respect!edit elementor-pro/modules/woocommerce/module.php
after line 822 : public function e_cart_count_fragments( $fragments ) {
add the following:
if( ! $this->use_mini_cart_template ) return $fragments;
Taken from previous post here:
Thanks @AviWEB for this fix
Tried not workingThis incompatibility still plagues us and this fix is essential still in 2023 June - man I tell you someone wrote earlier "not all heroes wear capes" well jkrolling man I just want to say again how much I appreciate that you shared this fix because from what I see it's nowhere on the web and this one line fixes the minicart being broken on one of my customer sites who use Porto as their theme. Without this one line modification to Elementor the minicart wouldn't work, it would just have a spinning icon and be unusable. Hopefully the Elementor devs will find more of these incompatibilities and fix their code but in the meantime I patch each version with this line and include a thankyou to jkrolling in the comments. Respect!
We get it, advertisements are annoying!
However in order to keep our huge array of resources free of charge we need to generate income from ads so to use the site you will need to turn off your adblocker.
If you'd like to have an ad free experience you can become a Babiato Lover by donating as little as $5 per month. Click on the Donate menu tab for more info.

